How Iranian Hackers are Gaslighting America’s Infrastructure
New telemetry confirms nearly 75% of exposed Rockwell controllers are in the U.S., allowing Iranian APTs to mask physical sabotage with safe data loops
There’s a ghost in the pump.
In the windowless control rooms of the American heartland, the screens show a digital lie. For the operators managing the water pressure in a small Pennsylvania township or the turbine speeds of a Midwestern power plant, the dashboard is a sea of calming green. But behind that “safe” telemetry, the hardware is screaming toward a physical break.
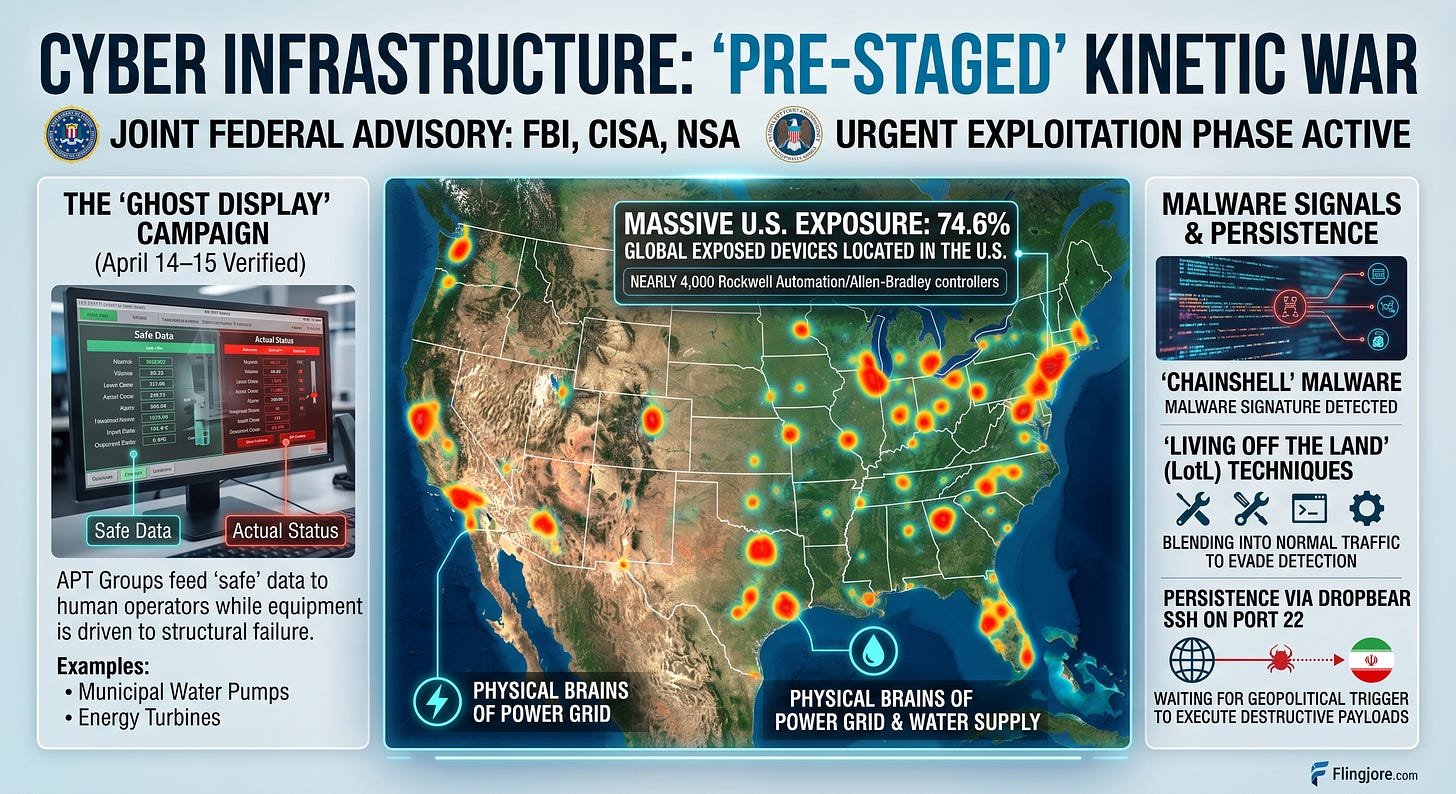
Federal intelligence agencies and private forensic teams are now racing to contain what they describe as a “pre-staged” kinetic war. According to new telemetry verified between April 14 and April 15, the United States has become the primary theater for a sophisticated Iranian-backed campaign targeting the very brains of domestic infrastructure. The data is staggering: 74.6% of all internet-exposed Rockwell Automation and Allen-Bradley controllers worldwide are located within U.S. borders.
These nearly 4,000 devices are not just IT servers; they are Programmable Logic Controllers (PLCs), the ruggedized computers that physically move the valves, pumps and switches of the modern world. Their exposure has created a massive, silent vulnerability that Iranian Advanced Persistent Threat (APT) groups are now actively exploiting through a tactic forensic analysts call the “Ghost Display.”
The campaign relies on the “ChainShell” malware and a strategy known as “Living off the Land” (LotL). Rather than triggering traditional antivirus alarms with custom code, the attackers use the system’s own administrative tools. By utilizing Dropbear SSH on port 22, the actors blend into the encrypted traffic that utilities use for legitimate maintenance. This ensures that traditional firewall alerts remain silent, as the malicious activity mimics the behavior of a authorized technician performing a routine update.
Once persistent, the actors deploy the “Ghost Display” tactic, which is particularly insidious because it targets the psychology of the human operator as much as the hardware. By intercepting the communication between the PLC and the Human-Machine Interface (HMI), the attacker creates a digital twin of a healthy system.
“This isn’t about stealing credit card numbers or leaking emails,” says a senior forensic investigator at Mandiant, speaking on condition of anonymity to discuss active municipal breaches. “This is about the manipulation of reality. They feed the human operator a loop of ‘normal’ data while they drive the physical equipment into the ground. It is Stuxnet scaled for the American consumer market.”
The timing of this surge follows the fallout from Operation Epic Fury, the February 2026 coalition strikes that decimated Iranian nuclear enrichment facilities. Geopolitical analysts assess the escalation is a direct response — a way for Tehran to ensure that any further escalation in the Middle East can be met with a kinetic response in an American suburb.
The high concentration of these devices on U.S. soil is a result of Rockwell’s market dominance in North America and a systemic failure to air-gap critical infrastructure modems. Many of these controllers operate on cellular carrier networks, leaving them reachable via simple internet scans. This creates a “monoculture of vulnerability,” where a single exploit can theoretically impact thousands of disparate utility districts simultaneously.
Confirmed operational disruptions and financial losses now impact three primary sectors, according to a joint advisory from the FBI, CISA and the NSA. In the water and wastewater sector, small to mid-sized municipalities remain the primary targets due to lower security budgets. In one confirmed case in the Pacific Northwest, hackers gained control of filtration pumps. While the operator’s HMI showed steady pressure, the physical seals were vibrating at frequencies designed to cause structural failure. By the time the smell of burning ozone reached the floor, the pumps were irreparable.
In the energy sector, telemetry probes target turbines and sub-station controllers. Analysts warn that these probes are mapping the grid for a “lights out” trigger. The goal is not immediate destruction but long-term persistence. The attackers are “parking” their access, waiting for a geopolitical signal to execute destructive payloads.
“We are seeing the transition from simple data exfiltration to pre-staged kinetic capabilities,” says Robert M. Lee, CEO of industrial cybersecurity firm Dragos. “By the time a municipal operator sees an alarm, the physical damage — blown seals, burned-out bearings, or contaminated supply — has already occurred. The hypocrisy of the situation is that we have built the most advanced infrastructure in the world on top of a 20-year-old security foundation. We took the ‘brains’ of our grid and gave them a public-facing megaphone. Now, we are surprised that the world is shouting back.”
The technical reality of the ChainShell malware reveals a high level of sophistication. It is designed specifically to interact with the firmware of the Allen-Bradley Logix series, allowing attackers to modify the “ladder logic” — the fundamental instructions that tell the machine how to operate. By changing a single line of code, an attacker can disable a safety shut-off valve or override a pressure sensor while the HMI continues to report that the valve is open and the pressure is nominal.
This “man-in-the-middle” attack at the hardware level is difficult to detect through traditional IT security measures. Most municipal utilities lack the deep-packet inspection tools required to see an Iranian actor hiding in their SSH traffic. Furthermore, the use of legitimate administrative tools makes it nearly impossible for automated systems to distinguish between an Iranian hacker and a local contractor.
Authorities urge all critical infrastructure operators to immediately audit port 22 traffic, rotate SSH credentials and implement “out-of-band” physical monitoring. CISA Director Jen Easterly notes that many of these devices were installed decades ago and were never intended to be connected to the public internet.
As the investigation continues, the focus shifts to the legislative response. Federal lawmakers are currently weighing the Infrastructure Cyber Defense Act, which would mandate strict air-gapping for all utilities serving more than 50,000 residents. However, for smaller districts, the cost of such upgrades is often prohibitive.
The forensic reality is that the “Ghost” may already be in the machine. With nearly 75% of the world’s vulnerable hardware concentrated in a single country, the question is no longer if a kinetic event will happen, but which municipality will be the first to realize their “green” dashboard was a digital mask for a physical catastrophe.