DHS awards Palantir $139M contract for ICE surveillance system through 2026
Renewal secures Investigative Case Management (ICM) platform four more years, raising Fourth Amendment concerns over mass data aggregation and digital privacy.
The Department of Homeland Security (DHS) has quietly cemented the technological infrastructure for mass immigration enforcement, awarding Palantir Technologies a contract worth more than $139 million to operate and enhance its Investigative Case Management (ICM) system.
The agreement, detailed in federal contracting records, secures the data-mining giant’s role as the central nervous system of Immigration and Customs Enforcement (ICE) operations through at least April 2026. While the contract is framed as a routine renewal for operations and maintenance, privacy advocates and legal scholars argue it represents a fundamental shift in American law enforcement: the normalization of a digital general warrant that subjects millions of people — citizens and non-citizens alike — to algorithmic scrutiny without individualized suspicion.
The deal covers the Investigative Case Management (ICM) platform, a core surveillance tool that aggregates vast amounts of data from federal, state and commercial sources into a single, searchable interface. The total potential value of the contract, if all options are exercised, rises to approximately $159 million.
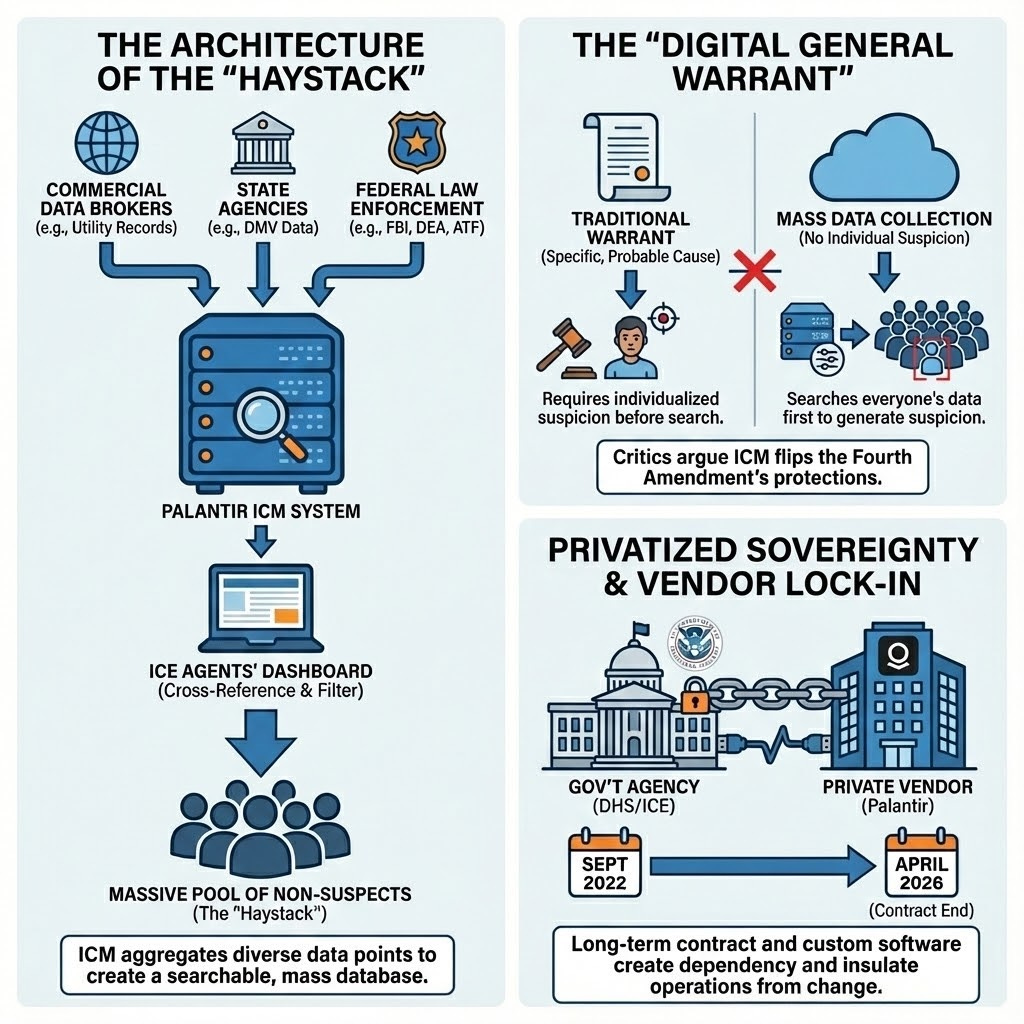
Architecture of the Haystack
The ICM system is not merely a digital filing cabinet; it is an engine for connecting disparate data points. According to contracting documents and previous agency disclosures, ICM allows agents to cross-reference data from the FBI, Drug Enforcement Administration (DEA) and Bureau of Alcohol, Tobacco, Firearms and Explosives (ATF) with private sector data streams.
This aggregation capability is central to what security agencies often describe as the Haystack theory of policing: to find the needle (a specific target), the government argues it must possess the entire haystack (the total population’s data).
“Palantir is the corporate backbone of ICE,” said Hannah Lucal, a fellow at Just Futures Law, noting that the software is used in day-to-day operations for surveillance and deportations.
The reach of this haystack is vast. A report by the Georgetown Law Center on Privacy & Technology estimated that ICE has access to the driver’s license data of three in four American adults. By ingesting this data into platforms like ICM, ICE can bypass the traditional investigative process. Instead of starting with a suspect and gathering evidence, the system allows agents to start with a massive pool of innocent people and use algorithms to filter for targets.
Digital General Warrant
The Fourth Amendment was drafted specifically to ban general warrants — broad writs used by the British Crown to search anyone, anywhere, without specific reason. Legal analysts warn that the ICM system functions as a modern, digital equivalent of these prohibited tools.
“The Fourth Amendment traditionally requires individualized suspicion,” said a legal analyst familiar with digital privacy case law. “This technology flips that standard. It allows the government to search everyone first to generate suspicion later.”
This inversion of constitutional norms relies heavily on the Third-Party Doctrine, a 1970s-era legal theory holding that individuals have no reasonable expectation of privacy in information they voluntarily share with third parties, such as banks or phone companies.
However, the Supreme Court’s 2018 ruling in Carpenter v. United States signaled a shift, recognizing that the aggregation of digital data — specifically cell site location information — reveals the privacies of life in a way that traditional records do not. Despite this ruling, DHS continues to purchase and aggregate commercial data that it would otherwise need a warrant to obtain, effectively purchasing its way around the Bill of Rights.
Privatized Sovereignty and Vendor Lock-In
The structure of the Palantir contract highlights another deepening trend: the privatization of state capacity. The contract includes funding for custom software enhancements, indicating that the government is not just buying a product but paying a private vendor to shape the architecture of federal law enforcement.
This dynamic creates vendor lock-in, where the agency becomes so dependent on a specific contractor’s proprietary algorithms and data structures that it cannot switch providers or bring the function in-house without crippling its operations.
The contract’s duration, running through April 2026, ensures that this surveillance architecture will remain in place regardless of short-term political shifts. It effectively insulates the enforcement machine from the democratic process, locking in a specific mode of policing that relies on high-tech surveillance.
Civilizational Erasure via Data
While the immediate focus of the ICM system is immigration enforcement, the implications extend to the broader concept of civilizational erasure — not of a specific culture, but of the private sphere itself.
By converting the daily activities of millions of people — utility usage, movement patterns, license plate scans — into searchable government records, the system erodes the boundary between the state and the citizen. The end of history for privacy is not a dramatic event but a bureaucratic one, signed into effect via procurement orders like contract #70CTD022FR0000170.
The potential for mission creep is built into the system’s design. Originally justified for counter-terrorism and serious transnational crime, these tools are increasingly used for routine civil infractions. Contracting records show that the system is used to track visa overstays and other administrative violations, deploying military-grade intelligence tools against non-criminal populations.
Costs of Control
The financial cost of this surveillance is explicit: $139 million committed, with a ceiling of nearly $160 million. However, the social cost is more difficult to quantify.
Critics argue that the true cost is the degradation of trust in essential services. When utility records and DMV data become arms of the state surveillance apparatus, vulnerable populations — and eventually the broader public — may withdraw from civic participation to protect their privacy.
As DHS moves forward with the ICM contract, the infrastructure for a total surveillance state is being laid not in secret, but in the open pages of federal spending logs. The question remains whether the legal frameworks of the 18th century can withstand the data mining capabilities of the 21st century



Trump, as always, he is following in other fascists footsteps, and the whole ICE brown shirts, Gestapo tactics with using billionaire Peter Theil's Palantir surveillance network, is par for the course and Theil, he is another fascist like Trump, who wants American democracy to be gone! where only the rich survive with dignity and freedom and everyone else as serfs and it is Thiel, who among the many awful things, has said, the democracy is not compatible with capitalism and should end. The word, capitalism, in his context, is make money at the expense of everything and everyone else, so in that context of incompatibility, he is right.